Are Your Clients Ready?
Globally, 51% of Organizations Are Unprepared for a Cyberattack or Breach —
A recent survey of 800+ CISOs and other senior executives across North America, Europe, and Asia, uncovered attitudes towards some of cybersecurity’s most prevalent topics.
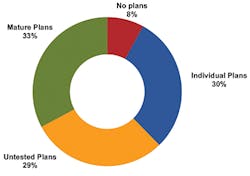
With the perpetually shifting threat landscape, most of the organizations surveyed (over 90%) believe that the cyberthreat landscape will stay the same or worsen in 2020. Further, the majority (51%) of organizations do not believe they are ready for or would respond well to a cyberattack or breach event. Moreover, 29% of organizations with cyberattack and breach response plans in place have not tested or updated them in the last 12 or more months. (See Figure 1.)
Cyberattack and Breach Response Plans
Figure 1.
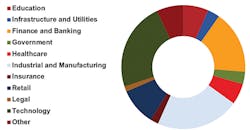
Nearly a dozen industry segments were represented in the study. The top 3 industries — technology, industrial and manufacturing, and banking and finance — accounted for 71% of all participants. (See Figure 2.)
Participant Industry Segment
Figure 2.
Globally, 53% of participants reported into the IT organization, 20% reported to business operations, 13% to finance, 11% to a dedicated cybersecurity function, and 4% to legal. In the US, the breakdown was more pronounced with 78% reporting to IT, 10% to business operations, 6% to finance, 4% to cybersecurity, and 2% to legal. (See Figure 2.)
Figure 2.
Investment Priorities
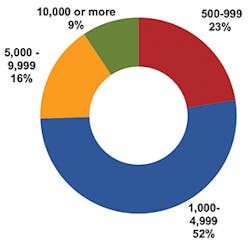
To address concerns regarding the potential loss of sensitive data, customer impact, and business operation disruptions, the vast majority (76%) of organizations plan to increase their cybersecurity budget in 2020. (See Figure 3.)
Planned Budget Change for 2020
Figure 3.
• Organizations most commonly expressed plans to bump cybersecurity spending by 1-9% over 2019 allocations.
• Cybersecurity budgets are focused on 4 main categories: prevention (42%), detection (28%), containment (16%) and remediation (14%).
• The greatest number of US participants indicated budgetary increase plans of 10% or more (39%), followed by the UK (30%) and South Korea (22%).
• However, 25% of organizations in Japan and 24% in South Korea indicated plans to keep their security spend the same year-over-year.
InvisiLight® Solution for Deploying Fiber
April 2, 2022Go to Market Faster. Speed up Network Deployment
April 2, 2022Episode 10: Fiber Optic Closure Specs Explained…
April 1, 2022Food for Thought from Our 2022 ICT Visionaries
April 1, 2022THE ADDITIONAL FACTS LISTED HERE shed light on some of the more differentiated global viewpoints about cybersecurity and changes needed for the future:
• Globally, organizations allocate their cybersecurity budgets into 4 main categories, with the largest allocations going to the areas of prevention (42%) and detection (28%), followed by containment and remediation. Japan was the only country to break away from this order, expressing a greater emphasis on detection (40%) and then prevention (35%).
• US organizations take the lead in fully transitioning to the cloud. US organizations reported being furthest along in adopting a cloud-first approach with 37% having finished a complete cloud migration.
• Over 44% of global respondents expressed having transitioned some of their environment to the cloud, and that they were monitoring cautiously. Additionally, 35% had transitioned some of their environment with plans to continue, and 17% had completed a full cloud deployment.
• Germany and Japan participants express concerns regarding cloud security. Of the responding participants globally, 45% felt that the cloud was about as secure as on-premises, and a further 33% believed that the cloud was more secure. However, in both Germany and Japan, 24% of responding organizations perceived the cloud as being less secure — highlighting a disparity from the global average (18%).
• Globally, participants consistently identified the same solutions as having the most positive impact on their organization’s ability to prevent a cyberattack. Vulnerability management and security software took the lead (slightly above 16%). Employee training was the third (14%) followed by response plans and security hardware (both slightly above 12%).
The People Factor
France participants were the only ones of all global respondents to identify employee training as their top priority, if they did not have constraints. Furthermore, the research revealed that only 1% of organizations surveyed in France do not have an employee cybersecurity training program in place, compared to the global average of slightly above 11%.
In contrast, 25% of organizations in Germany and 23% in Canada report not having employee cybersecurity training in place. These numbers are especially concerning considering that a cyberattack can often result from just 1 employee clicking on a single hyperlink.
Finding a Balance
Organizations universally reported that it was more difficult to find a balance between cybersecurity and operational requirements, with 14% reporting it to be very difficult and 49% difficult. Only 14% of organizations found it easy, and 3% found it easier, to find a balance. Globally, 18% of organizations were neutral on the issue.
Participants from Japan reported that 54% of their organizations found it difficult, and 18% very difficult, to find a balance between cybersecurity and operational requirements, as did organizations in Germany with 53% reporting difficult and 13% more difficult.
In France, 26% of organizations reported that it was neither easier nor more difficult than before to find a balance between cybersecurity and operations requirements.
There were no significant regional differences for organizations that indicated it was easy or easier to find a balance between security and operations; they corresponded closely to global results.
Participants were asked to identify the top 3 components they believed to be the most likely targeted by cyberattacks, and which top 3 components they believed were the most likely to be vulnerable to a cyberattack. Participants were globally consistent in their belief that servers, server operating systems, and web servers; medical devices; and endpoints; were the top 3 components in both categories.
Security Program Maturity
When assessing their cybersecurity programs, 27% of participants characterized them as semi-formal approaches where efforts were mostly compliance-driven and focused on addressing mandatory regulations, while 24% saw their programs as informal where the primary focus was addressing critical issues as they occurred.
Globally, 23% of organizations reported formal security programs with a broad, risk-based focus supporting continuous optimization of processes and approaches, compared to the US (41%) and China (38%).
Only 19% of organizations identified their security program as strategic with intelligence data driving investment decisions, operational priorities. and other critical cybersecurity factors.
Overall, 7% of organizations indicated they did not have a cybersecurity program at all.
Like this Article?
Subscribe to ISE magazine and start receiving your FREE monthly copy today!
This article was adapted from FireEye Cyber Trendscape Report. This research study was commissioned by FireEye and delivered by Kantar, an independent market research organization. Results were derived from an online survey fielded in July-August 2019 for a total of over 800 responses spanning across North America (US and Canada), Europe (France, Germany and the UK) and Asia (China, Japan and South Korea). Setup questions were used to ensure that only cybersecurity executives were in the sample, which was defined as those at the C-level or above, Vice President, or Senior Director level. For more information, and to download the report, please visit https://www.fireeye.com/offers/rpt-cyber-trendscape.html.